Things weren’t working as expected
I had recently enabled the SSL Deep Inspection policy on some of my web traffic - in part to try to block ads, maybe I’ll write a blog post about that another time - and I was noticing odd behaviour.
A few of the odd things were around VPN connections and Citrix sessions.
FortiClient VPN wasn’t able to connect - it was getting to 80% then throwing an error saying there was something wrong w/ my credentials or my account wasn’t setup for VPN access.
With Citrix, apps would look like they were launching from the StoreFront, but they wouldn’t load - they wouldn’t even briefly show up in the connection manager. Launching a published desktop it would load the app’s borders, but then throw an error.
Once I saw the Citrix published Desktop error, I was pretty sure I knew the source.
But I’d already installed the cert the FortiGate was using
I had installed the FortiGate’s cert as a Trusted Root CA Cert on my laptop, so I was expecting the traffic would be fine. However, I needed to exclude the sites from the SSL Inspection rule. Once the exclusion was in place everything started working again.
To add the sites, expand Security Profiles - SSL/SSH Inspection.
Select the policy in use, and scroll down to the “Exempt from SSL Inspection” section.
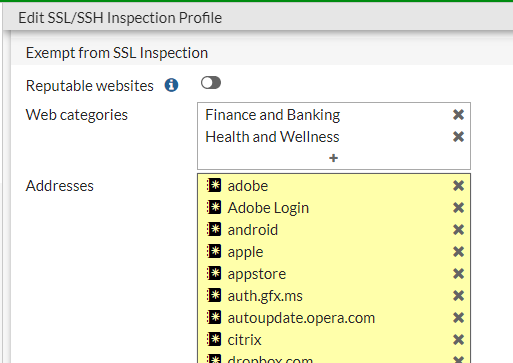
You can exempt entire web categories, but I needed to exempt addresses.
To create a new address, click the “+” at the bottom of the addresses column, this will open the “Select Entries” panel, click the “+ Create” button to add a new entry. From the options, I needed to select Wildcard FQDN for each of the client’s URLs.
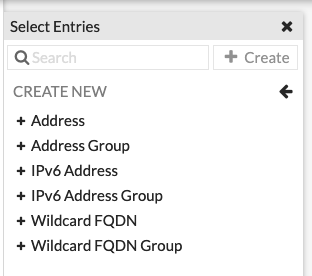
Give the new address entry a name, enter the URL and hit OK. For the URL I used *.example.com. This will not take www.example.com, it will only accept * on the version of FortiOS I was working on.
Make sure to add the new address to the list of exclusions, then click Ok to update the policy.
You might need to close and re-open your browser for the FortiGate to stop swapping its cert in for the orginal.
